Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Cse.google.com took over your homepage and you cannot remove it.
A proxy virus is a rather unpleasant thing. It meddles with your proxy setting, and messes them up. It does that to trick you. Its goal is to deceive you into believing something untrue. In a nutshell, a proxy virus tries to pass a knock-off as the real deal. In our current case, it attempts to convince you that Cse.google.com is a legitimate website. And, NOT a mere imitation. That’s a lie. The site disguises something malicious and unreliable as useful and trustworthy. It’s dangerous to use it as it leads to more threats, slithering into your system. And, it also conceals a browser hijacker. It acts as a front, behind which lurks the hijacker. And, in case you’re unfamiliar, these infections are dangerous, intrusive, and quite damaging. Hijackers are hazardous and damaging to both your privacy and your PC. Don’t underestimate the troubles a hijacker can, and will, throw your way! Its parade of disaster begins, innocently enough, with mere annoyances. Like, the occasional pop-up ad appearing on your screen. Then, there’s an entire waterfall of them. Not to mention, the never-ending redirects to Cse.google.com. Or, the unwanted, unapproved reshuffled. Or, the malware risk. Or, worst of all, the security threat. Do you think the nasty hijacker, hiding behind the nasty Cse.google.com page, is worth that trouble? Protect yourself and your PC! Find the hijacker’s lurking place. And, when you locate it, get rid of it at once.
How did I get infected with?
Hijacker applications need your permission to enter your system. They have to ask whether you agree to install them. And, can only after you say ‘Yes.’ If you deny them – no admittance. In other words, you’re the architect behind your current predicament. Because the tool asked whether you consent to its install. And, you did. Otherwise, you wouldn’t be in this mess. So, how do you think the exchange went down? After all, the tool didn’t just come out in the open, and seek access to your PC. Did it? Well, it did and it didn’t. Let’s elaborate. Hijackers need your compliance to invade your system. But if they openly ask for it, you can deny them. So, that’s out of the question. They still ask you. They just do it the most covert way possible. For example, the cyber threat can pose as a bogus update. Like, Java or Adobe Flash Player. Or, hide behind corrupted links or websites. Or, hitch a ride with freeware or spam email attachments. So, you see. The tool still, technically, asks for your stamp of approval on its installation. It just does it cloaked, hiding behind various means of infiltrations. If you wish to spot it trying to slither in, be more careful! Don’t throw caution to the wind, and don’t rush. Infections prey on carelessness and gullibility. So, don’t provide them.
Why is this dangerous?
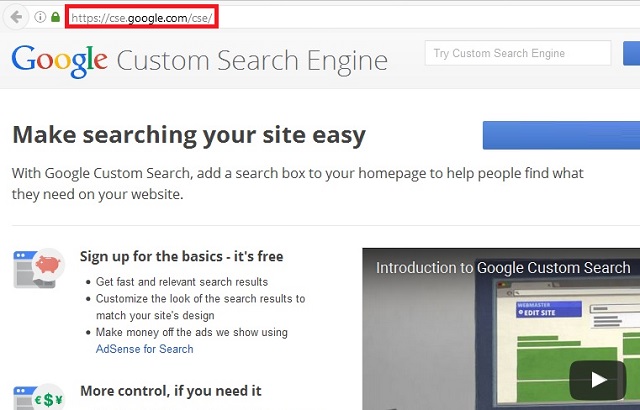
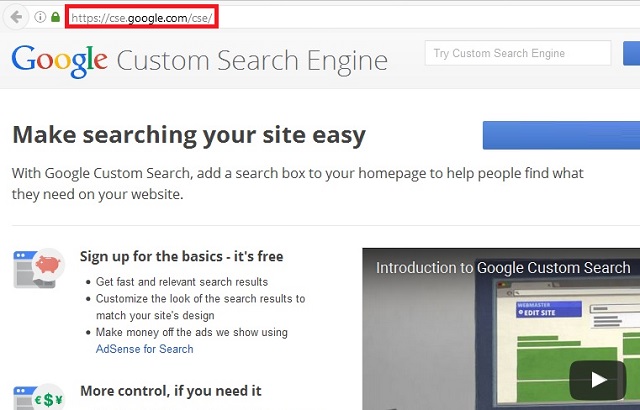
Cse.google.com may contain the word ‘google’ in its name, but make no mistake! That’s a desired effect to dupe you, the user, into buying the page’s legitimacy. But it’s far from legitimate. It has nothing to do with Google! It’s a malicious domain, exploiting the naivety of the masses! The people, who think that just because it has ‘google’ in the name, it must be connected to the real thing. Well, it’s not. Cse.google.com is an impostor. The page was designed by individuals, who saw an opportunity, and grabbed it. But, we say again. Cse.google.com is a malevolent page, which brings only negatives and headaches. It promises the world but delivers nothing. It falls short on each promise. Cse.google.com does NOT “Make searching your site easy.” In fact, it makes searching the web quite the dreaded experience. Why? Well, the hijacker behind the website follows certain programming. Shortly after infiltration, it replaces your default search engine and homepage with Cse.google.com. It also redirects you to the site each time you use your browser. And, that’s following the flood of pop-up ads, you’ll also have to endure. But that’s not the only annoyance, you’ll suffer through. As was already mentioned, the ads and redirects cause further frustrations. Due to their constant meddling, your computer slows down to a crawl. And, your system starts to crash all the time. But even if you exhibit tunnel vision, and put up with all these issues, there’s one you just can’t ignore. And, that’s the security threat. The hijacker, lurking on your PC, spies on you. It keeps a close eye on your online activities, and catalogs your every move. It collects data from you. After it deems it has gathered enough, it sends it to the people that published it. Strangers. Unknown individuals with questionable intentions. Those are the people that will have access to your personal and financial information. The question is, are you going to let them have it? Or, are you going to protect yourself and your system? Make the right choice. Pick the latter, and get rid of the infection ASAP.
How to Remove Cse.google.com virus
If you perform exactly the steps below you should be able to remove the Cse.google.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Cse.google.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Cse.google.com from Add\Remove Programs
STEP 2: Clean Cse.google.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Cse.google.com leftovers from the System
STEP 1 : Uninstall Cse.google.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
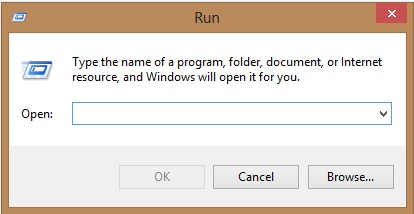
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Cse.google.com homepage from Chrome, Firefox and IE
-
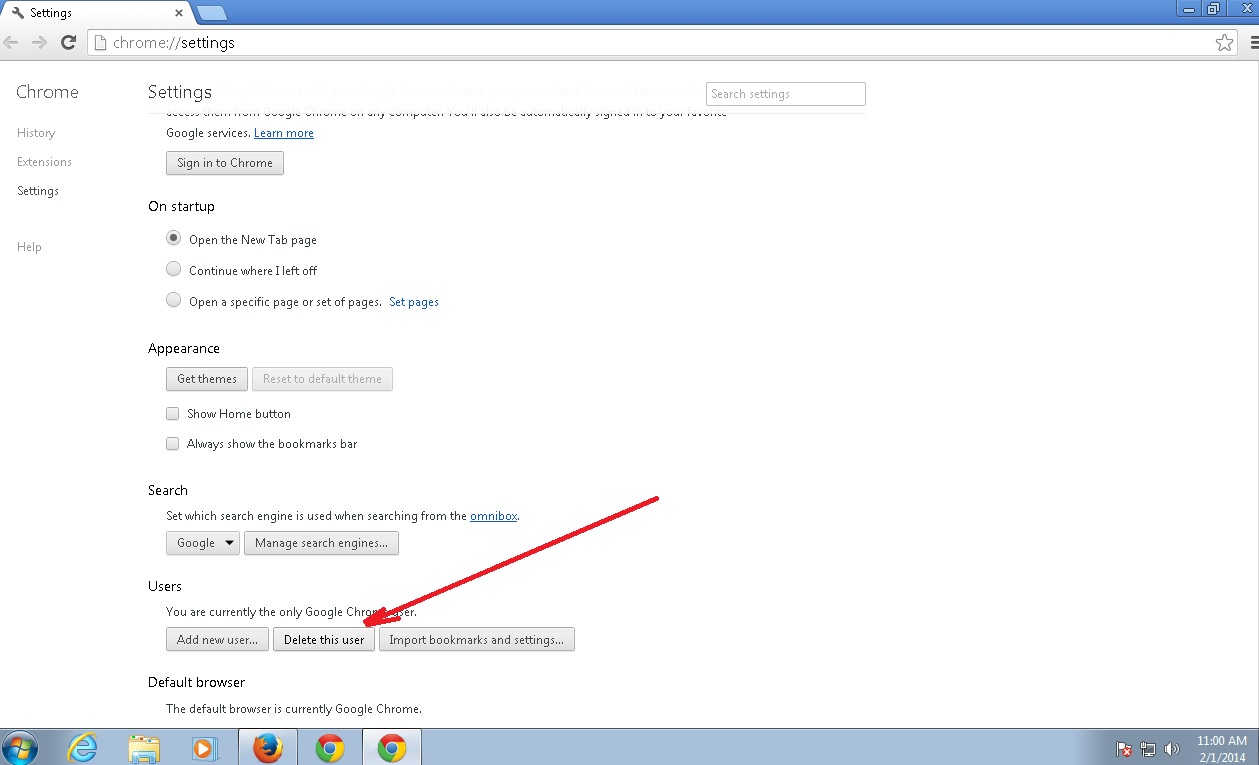
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Cse.google.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
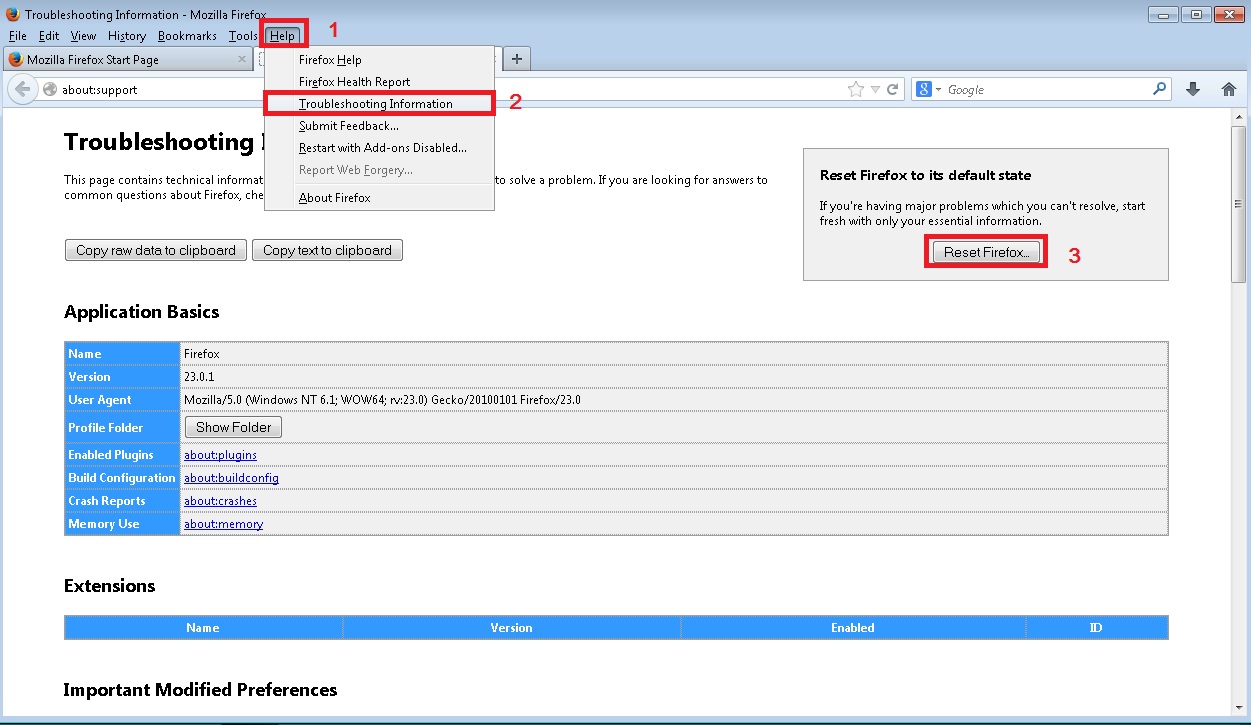
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
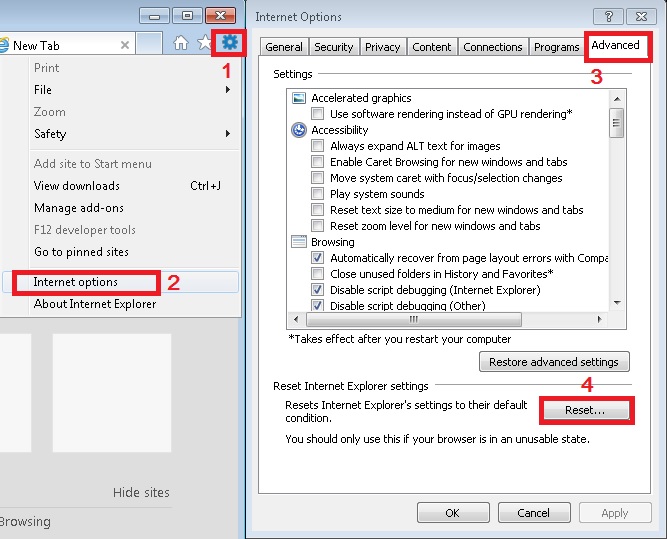
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Make sure your Windows HOSTS file is clean
- open your explorer and Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

You need to remove the poisoned IPs and save the HOSTS file.
Check your internet connection settings
- Right-click on the active Network Adapter, Click on Properties
- Navigate to Internet Protocol Version 4 (ICP/IP), click Properties.
- Click on Advanced and then navigate to the DNS TAB. The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
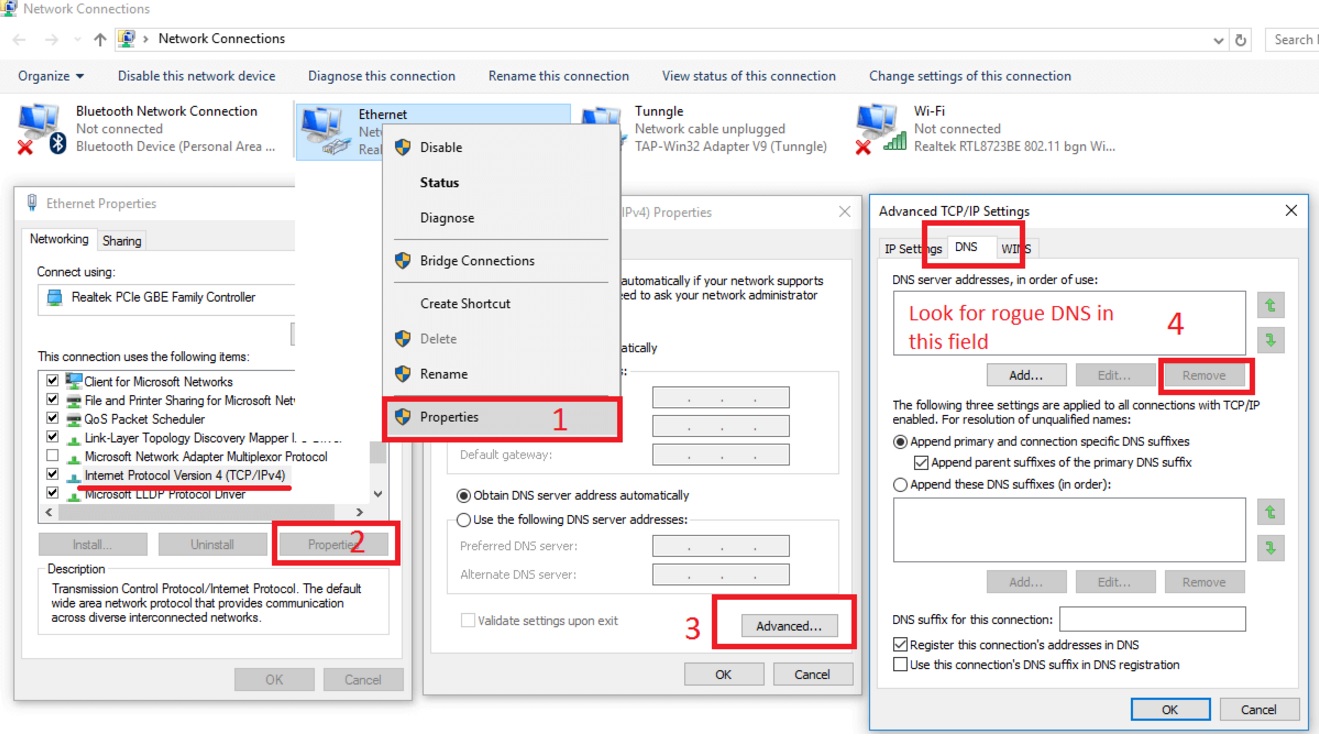
Double check your proxy settings as the malware is capable of modifying them.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for example, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
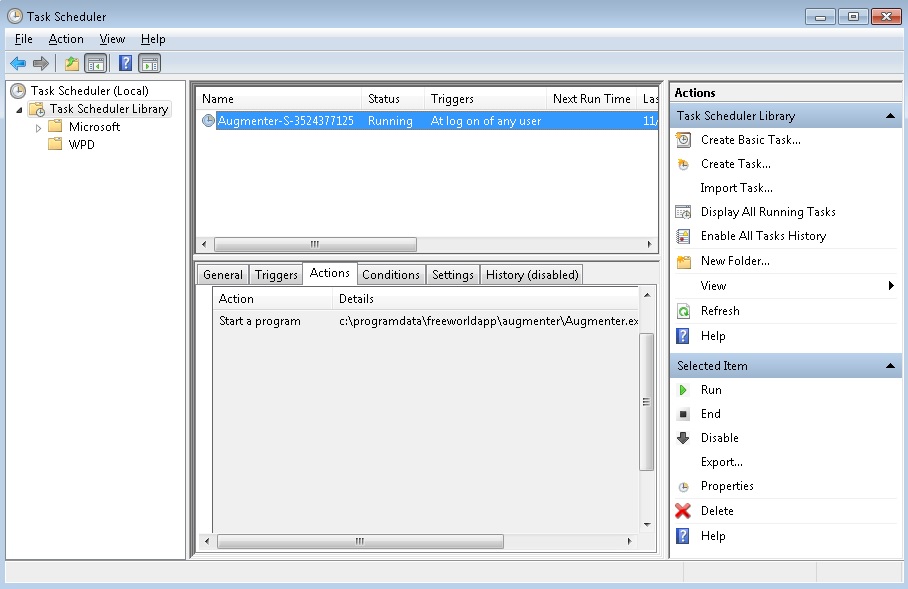
Check your Scheduled Tasks
- Open your windows task scheduler and delete any suspicious program. Usually, adware applications hide their droppers in here. Even if you remove the whole infection from the system files – the dropper will regenerate everything and the nightmare will start again.
How to Permanently Remove Cse.google.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.