Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Anasayfa.im took over your homepage and you cannot remove it.
Anasayfa.im is a page that brings bad news. If you see the site, your system’s no longer infection-free. You’ve managed to catch a nasty cyber threat. And, the appearance of the malicious domain is a sure sign of that. The Anasayfa.im site conceals the presence of a browser hijacker. Think of the page as a front. The infection uses it as a shield to hide behind, and wreak havoc from the shadows. And, does it ever! The hijacker doesn’t waste time. Pretty soon after it invades your system, issues start to flow. You’ll experience countless intrusions, reshuffles, and altogether grievances. You’ll get surprised with changes, which you did not authorize. And, your browsing will never be the same. The hijacker interferes incessantly. Every time you open a new tab or surf the web, there they’ll be! Redirects to various unreliable pages, as well as a flood of pop-up ads. And, as you can imagine, these constant disruptions won’t go unnoticed for long. They’ll slow down your computer, and cause frequent system crashes. Also, you’ll face a severe malware risk. Everything the infection displays is unreliable! Each pop-up and every link can potentially lead to the installment of more unwanted malicious tools. So, don’t pres anything it shows you! But even if you manage to avoid the ads, the sites, which the hijacker forces your way, you’re far from safe. The infection, using Anasayfa.im as a face, jeopardizes your privacy. It threatens to steal and expose your personal and financial information to strangers. Are you going to let it? Make no mistake! If you take no action against it, or take your time, it WILL succeed! The sooner the hijacker is gone, the better! So, don’t delay! As soon as Anasayfa.im pops up, find the tool’s hiding place. And, when you do, get rid of it. Delete it upon discovery. You won’t regret it.
How did I get infected with?
As was already explained, if Anasayfa.im pops up, you have a hijacker on your PC. But how do you imagine it got there? This type of infection needs user’s approval to enter. Your approval. It has to ask whether you agree to its installment or not. And, if you deny it, it cannot install itself. In other words, you’re the reason for your current predicament. If you hadn’t granted entry to the hijacker, you wouldn’t get plagued by Anasayfa.im. So, the question is, how? How did you consent to install an infection? Well, it’s pretty straightforward. The program duped you. After all, it didn’t just show up and ask for your approval. What if you said ‘No?’ That’s a chance the tool cannot take. So, to ensure its successful invasion, it used deception and finesse. That’s right. Through slyness, it fooled you giving it the green light. Its trickery usually involves hiding behind freeware. Or, hitching a ride with corrupted links or spam email attachments. Or, posing as a bogus update. In a nutshell, it turns to the old but gold means of infiltration. But, whichever method it uses, it cannot succeed without your carelessness. So, don’t grant it. Be extra thorough and vigilant. And, always pick caution over naivety and haste.
Why is this dangerous?
Think of Anasayfa.im as a harbinger of trouble. If you see the site, you’re about to experience of bunch of issues. The infection, which is hiding behind the page, is dangerous and malicious. It’s invasive and meddling. And, its intrusiveness first shines through shortly after the hijacker sneaks into your system. All of a sudden, you find your homepage and search engine switched. The tool replaced them with Anasayfa.im. And, it did so without asking for your consent, or bothering to inform you. Well, get used to that feeling of surprise as the intrusions don’t end there. Hijackers can install malicious programs on your computer. And, yes! You’ve probably guessed it! They can do it without seeking your permission. So, even if you discard the other issues (which are a lot), don’t ignore this one. Not unless you wish to flood your system with unwanted malware. But, what’s even worse than the malware risk, is the security threat. As was already stated, the hijacker jeopardizes your personal and financial details. That’s because it keeps track of your every online move, and catalogs it. Once it decides it has enough information, hands it off to the people that published it. Don’t let that scenario unfold. It does not end well for you. Protect your privacy, as well as your PC, from the clutches of a dangerous cyber menace. As soon as you see Anasayfa.im for the first time, act! Find and delete the nasty hijacker, responsible for its appearance. It’s the best course of action you can take. Take it soon.
How to Remove Anasayfa.im virus
If you perform exactly the steps below you should be able to remove the Anasayfa.im infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Anasayfa.im adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Anasayfa.im from Add\Remove Programs
STEP 2: Clean Anasayfa.im from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Anasayfa.im leftovers from the System
STEP 1 : Uninstall Anasayfa.im from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
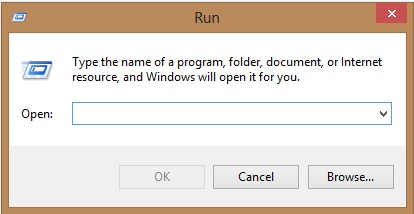
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Anasayfa.im homepage from Chrome, Firefox and IE
-
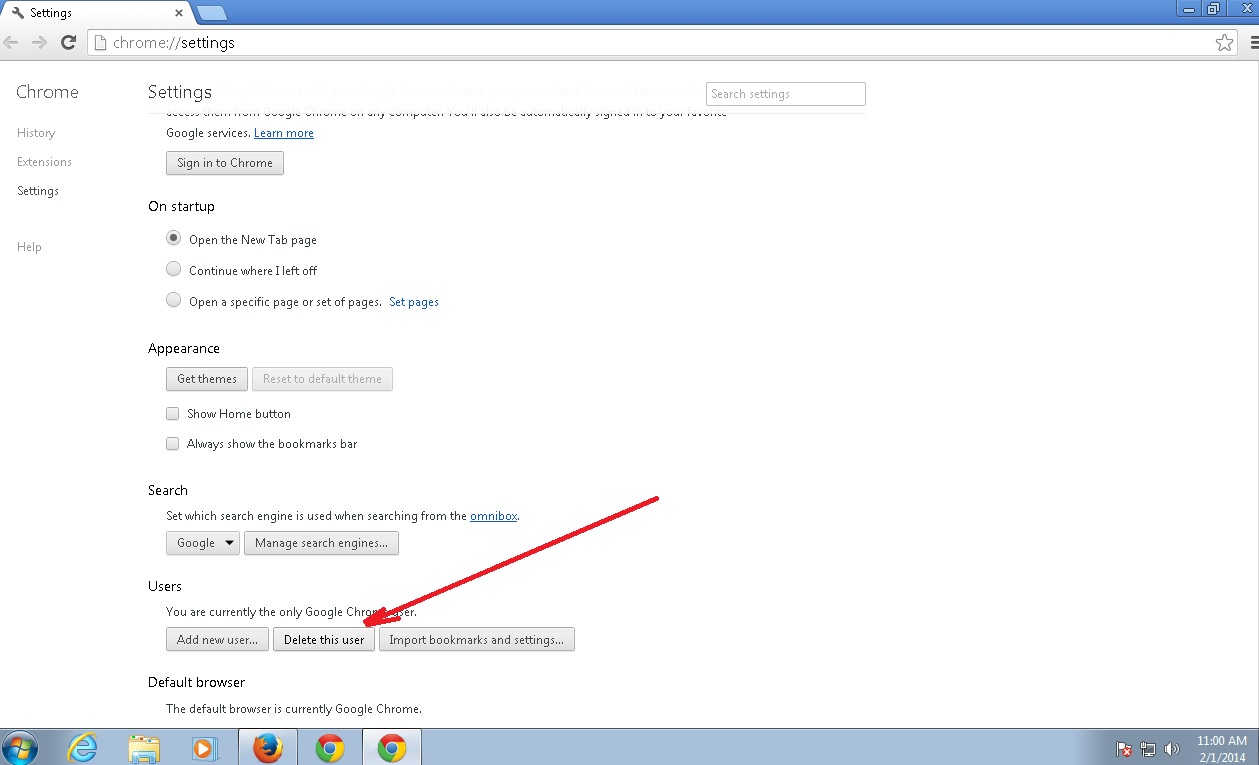
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Anasayfa.im by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
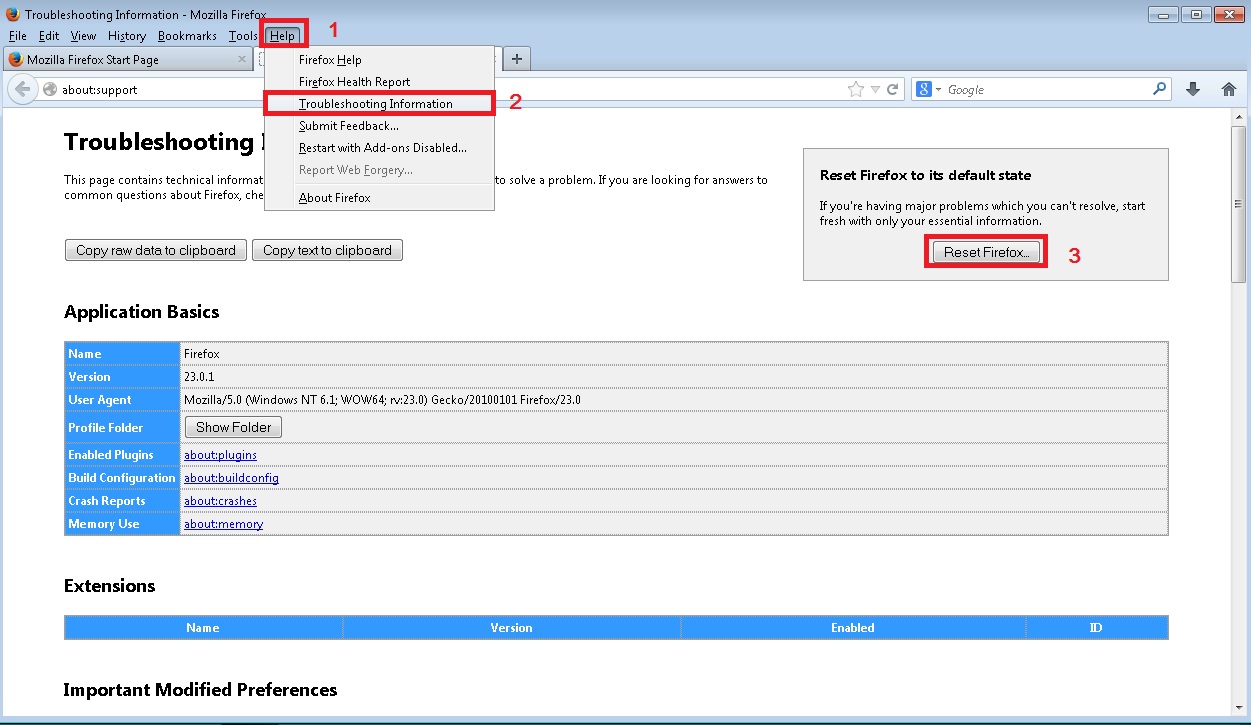
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
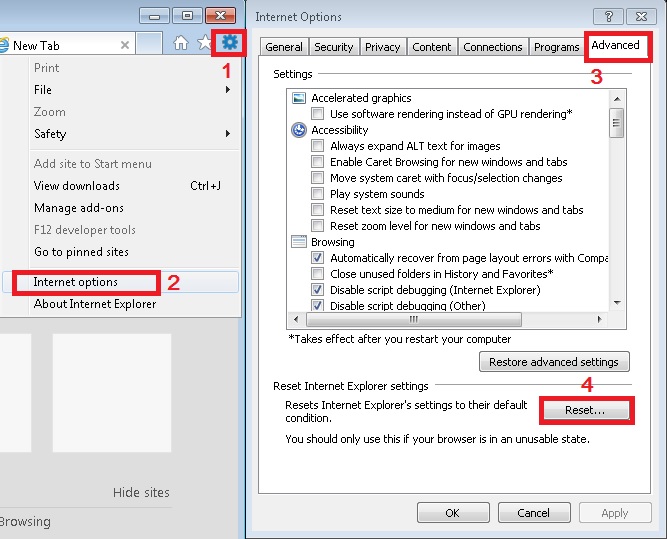
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Anasayfa.im Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.